Hardening WordPress
Hardening Recommendations
Below we propose structural changes that provide additional security hardening for your WordPress installation. Each option comes with some disadvantages and problems which you need to be aware of.
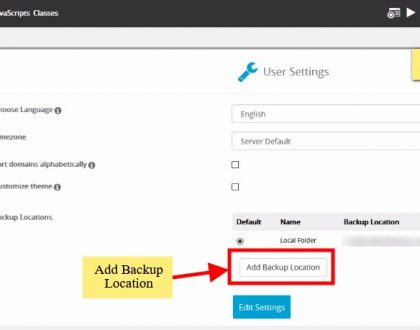
Data Backups
Back up your data regularly, including your MySQL databases.
A sound backup strategy could include keeping a set of regularly-timed snapshots of your entire WordPress installation (including WordPress core files and your database) in a trusted location.
Access Control
One of the top two attack vectors used by cyber criminals is software vulnerabilities and access control. To combat this you must secure any point of entry into your host, WordPress installation or server. This includes employing strong passwords and enabling some form of Multi Factor authentication.
2FA Authentication
When working with any online site, consider enabling 2FA by default. Refer to Two Step Authentication for more information.
Some WordPress plugins designed to help include:
Authy
Duo
Rublon
Two-Factor
Passwords
The goal with your password is to make it hard for other people to guess and hard for a brute force attack to succeed. A key to this is making it Complex, Long, and Unique. It is recommended to use a password generator for all passwords.
WordPress also features a password strength meter which is shown when changing your password in WordPress. Use this when changing your password to ensure its strength is adequate.
Services like 1Password and LastPass can help you manage and create random passwords.
Core Directories / Files – File Permissions
The default permission scheme should be:
Folders – 755
Files – 644
There a number of ways to accomplish this change. There are also a number of variations to these permissions that include changing them to be more restrictive. These however are the default recommendations. Check with your host before making permissions changes as they can have adverse affects on the performance and availability of your site.
Avoid having any file or directory set to 777.
You can read more about WordPress updates and file ownership on the Updating WordPress codex page.
Changing file permissions
Via command line you can run the following commands to change permissions recursively:
For Directories:
find /path/to/your/wordpress/install/ -type d -exec chmod 755 {} \;
For Files:
find /path/to/your/wordpress/install/ -type f -exec chmod 644 {} \;
You can also do this via your favorite FTP/SFTP client.
WP-Admin
Adding server-side password protection (such as BasicAuth) to /wp-admin/ adds a second layer of protection around your blog’s admin area, the login screen, and your files.
Note: This prevents normal site visitors from accessing /wp-admin/admin-ajax.php.
See the Resources section for more documentation on how to password protect your wp-admin/ directory properly.
WP-Includes
A second layer of protection can be added where scripts are generally not intended to be accessed by any user. One way to do that is to block those scripts using mod_rewrite in the .htaccess file. Note: to ensure the code below is not overwritten by WordPress, place it outside the # BEGIN WordPress and # END WordPress tags in the .htaccess file. WordPress can overwrite anything between these tags.
# Block the include-only files.
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteBase /
RewriteRule ^wp-admin/includes/ – [F,L]
RewriteRule !^wp-includes/ – [S=3]
RewriteRule ^wp-includes/[^/]+\.php$ – [F,L]
RewriteRule ^wp-includes/js/tinymce/langs/.+\.php – [F,L]
RewriteRule ^wp-includes/theme-compat/ – [F,L]
</IfModule>
# BEGIN WordPress
Note: This won’t work well on Multisite, as RewriteRule ^wp-includes/[^/]+\.php$ – [F,L] would prevent the ms-files.php file from generating images. Omitting that line will allow the code to work.
WP-Content/Uploads
The uploads directory is the one directory that will almost need to be writable by the web server. It’s where all files are uploaded remotely. You want to prevent PHP execution in this directory, you can do this by placing an .htaccess at the root of /UPLOADS using:
# Kill PHP Execution
<Files *.php>
deny from all
</Files>
Note: This can break your theme if it requires PHP execution in UPLOADS. If you apply it and the site breaks, remove it and the site will reappear.
xmlrpc.php
If you do not plan on using a mobile application to connect to your installation, you might consider turning off access to xmlrpc.php ( in .htaccess ):
<files xmlrpc.php>
order allow,deny
deny from all
</files>
Or:
<files xmlrpc.php>
require ip 127.0.0.1
</files>
WP-Config.php
If you use a server with .htaccess, you can put this in that file (at the very top) to deny access to anyone surfing for it:
<files wp-config.php>
order allow,deny
deny from all
</files>
Disable File Editing
It is recommended to disable file editing within the WordPress dashboard. WordPress has a constant that disabled this editing via the wp-config.php file. Append the following two lines to the end of your wp-config file:
## Disable Editing in Dashboard
define(‘DISALLOW_FILE_EDIT’, true);
Security Plugins
There are many security plugins available for WordPress that provide a wide range of security and hardening features. There are four types of security plugins, it’s important to differentiate between them because each are designed to solve different problems.
Prevention: Help protect you from hacks. They often include some form of Firewall solution.
Detection: Identify and notify if something is off and requires further inspection. This can come in the form of scanners and integrity checkers.
Auditing: Track and maintain an active log of all the activity on the site (i.e., track log ins, changes to themes and plugins, updates, etc..).
Utilities: Provide a suite of options designed to empower the user to make security-focused changes to their installation
As you think through your security posture, and look to integrate a security plugin, consider what you are trying to achieve and how that plugin helps you achieve that goal.
Website Firewalls
Website Firewalls allow you to proactively mitigate external attacks like exploitation attempts that try to abuse software vulnerabilities, brute force attacks that try to break into your admin panel, or denial of service attacks that try to kill the availability of your website. All real security threats.
There are two types of Firewalls to be mindful of. You have End-point and Cloud-based Firewalls.
End-point Firewalls are applied at the web server itself, and often managed by the host (unless you manage your own Dedicated / Virtual Server, in which case you will be responsible for your own). There are also application end-point firewalls, these are found in WordPress plugins (each using their own approach for integration).
Cloud-Based Firewalls reside off your web server and application. They introduce an intermediary layer off the local origin environment. Most notable cloud-based Firewalls function as a CDN and offer a globally distributed network.
Deploying a Website Firewall is quickly becoming the best way to stay ahead of today’s emerging threats. It’s not however a substitute for a bad security, it’s one piece of a larger framework that should be considered.
Continuous Monitoring
Deploy tools that allow you to maintain visibility into the overall security state of your site. There are a number of tools designed to help with this.
Free Online Scanners
Remote scanners look at a website as a user or search engine would.
Examples:
VirusTotal
Sitecheck
Unmaskparasites
Redleg AW-Snap
These can be automated by using plugins as well, examples:
Quttera Web Malware Scanner
iThemes Security
Application Scanners
Application scanners look at the files locally on the server. For WordPress, this is achieved by security plugins.
Examples:
VaultPress
Anti-Malware Security
Wordfence
If you’re running a server, you might consider:
ClamAV
Reputation Monitors
Reputation monitors are services provided by established brands like Google, Bing, etc… that have a vested interest in your website displaying unaltered data.
Google Search Console
Bing Webmaster Tools
Norton Webmaster Tools
Yandex Webmaster Tools
These tools is that they are free, they have a vested interest in your site being clean, and will notify you 24 – 48 hours in advance before blocking your site.
Uptime / Availability Monitoring
Services like UptimeRobot and Pingdom monitor website availability. They send you an alert via email, SMS or mobile application if your website goes down. You can monitor your site from multiple locations.
One of the features of some of these services offer is the ability to monitor web page changes. Websitepulse can tell you if a page has changed by a certain percentage. Using availability monitoring along with monitoring of page changes can give you an early warning if your website has been hacked. Often a hacker will change or deface your website and catching changes early can alert you within minutes of a hack.
File Integrity Monitoring
Monitoring filesystem changes can give you early warning of an intrusion. There are a number of WordPress plugins that will look at the application and help you identify if the integrity of files has changed.
Example:
File Changes Monitor
Wordfence
Sucuri Scanner
Recommended Posts
Backup your site to Google Drive & Dropbox
24th January 2021

Manage your sites with WordPress Manager
24th January 2021

6 Reasons Why You Should Backup Your Website
18th September 2018